DamCTF2021 - Imp3rs0nAt0r-1
Some dumb college student thought he was leet enough to try and hack our university using a school computer. Thankfully we were able to stop the attack and we confiscated the equipment for forensic analysis.
Can you help us figure out what their next moves are?File : UsrClass.dat
To read the file I downloaded ShellBags Explorer
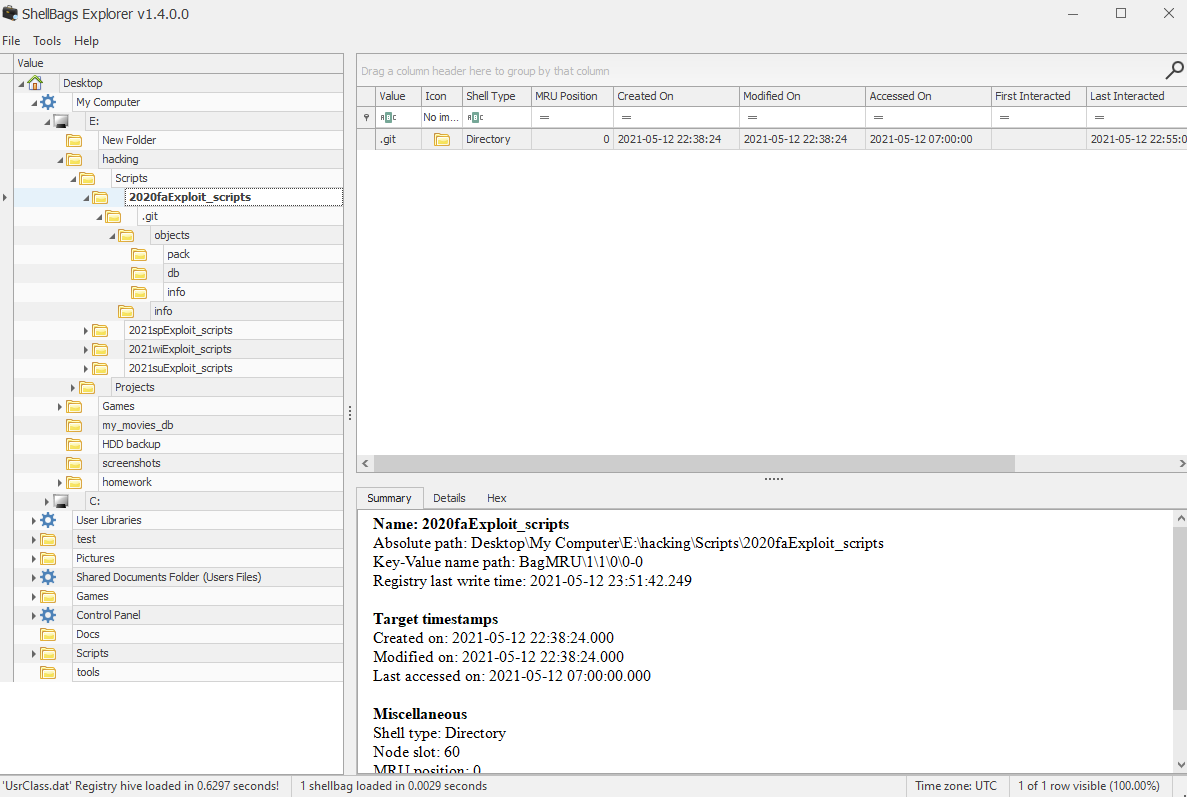
After loading the file, I found an interesting directory : E:/hacking/2020faExploit_scripts, I noticed a .git indicating that the project may use github. So I made a quick search on Google:
"2020faExploit_scripts" site:github.com
It directly found a github account and a project named h4ckerman-3000-bot, this project is a simple discord bot but the token of the bot was left in the project files.
import discord
import os
import random
client = discord.Client()
epic_hacking = [
"https://tenor.com/view/pc-hack-hacker-guy-fawkes-mask-gif-17047235",
"https://tenor.com/view/typing-fast-cyber-banana-help-gif-16125910",
"https://tenor.com/view/mega64-hacking-in-progress-hacker-hacked-hd-gif-16542434",
"https://tenor.com/view/hacker-game-over-laptop-hacking-hack-gif-17366041",
"https://cdn.discordapp.com/attachments/670767796925235252/842257131142250516/breenhacking.webm"
]
@client.event
async def on_ready():
print('We have logged in as {0.user}'.format(client))
@client.event
async def on_message(message):
if message.author == client.user:
return
if message.content.startswith('!hack'):
await message.channel.send(random.choice(epic_hacking))
token = base64.b64decode(b'T0RReU1qUTNPRFl6TWpVek56STVNamt3LllKeWljZy45SjI0aC11LUs1SmRQNFFPa2NRSmlOeXlaRHc=').decode()
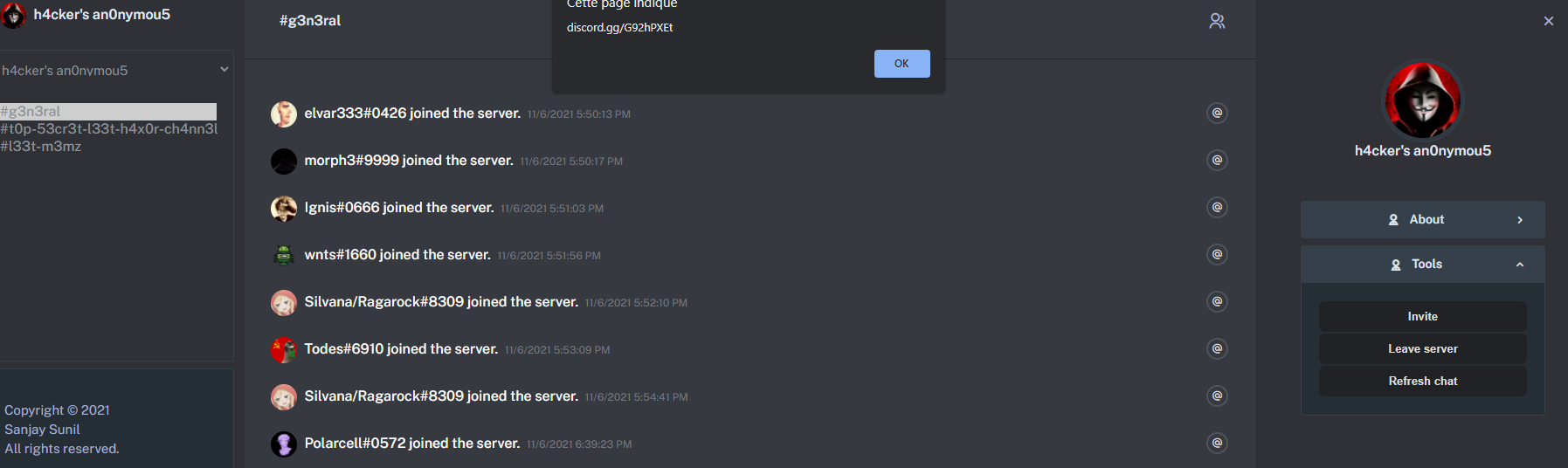
client.run(token)I found this project on github that allowed me to connect to a bot account on Discord : https://github.com/SanjaySunil/BetterDiscordPanel
So I used the client to create an invite to the discord server where the bot was connected :
I then joined the server and found in the message history the flag :
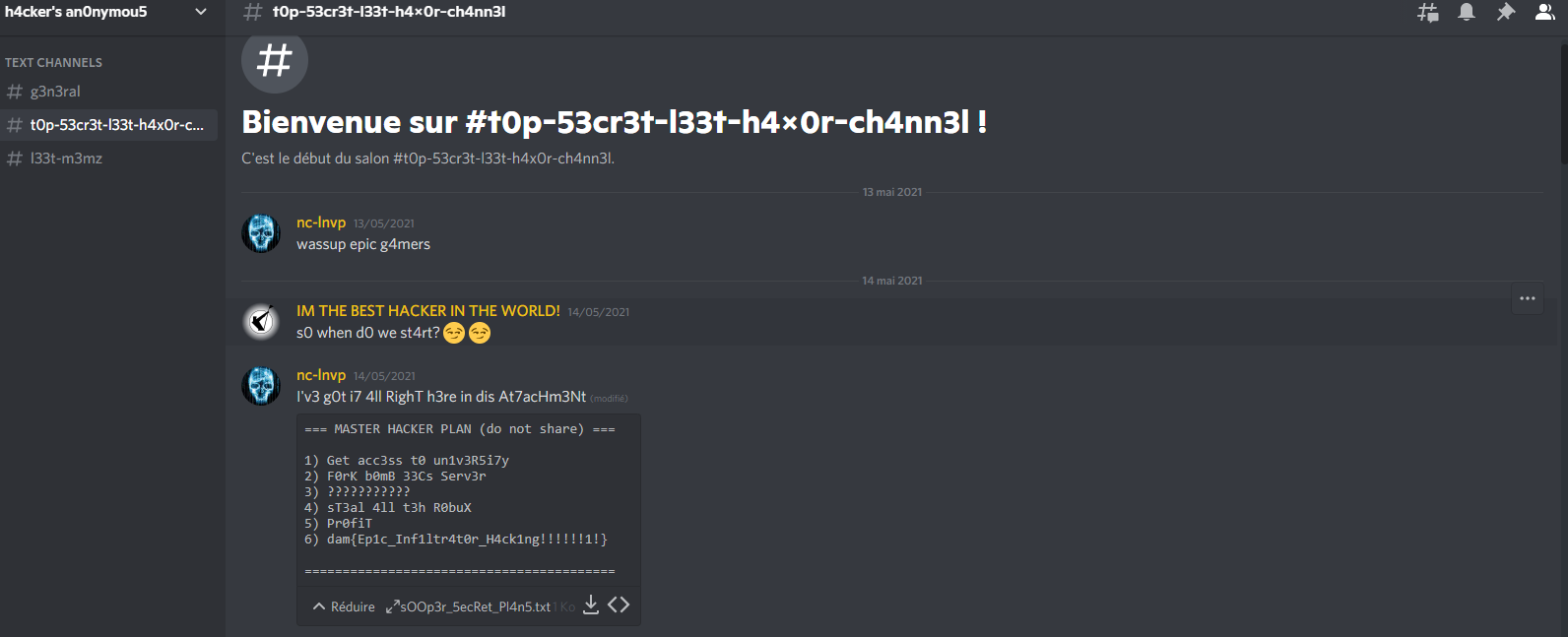
Here is our flag : dam{Ep1c_Inf1ltr4t0r_H4ck1ng!!!!!!1!}